Now Reading: Google’s Quantum AI Paper Cuts Bitcoin’s Encryption Timeline by 20X
-
01
Google’s Quantum AI Paper Cuts Bitcoin’s Encryption Timeline by 20X
Google’s Quantum AI Paper Cuts Bitcoin’s Encryption Timeline by 20X
- Google Quantum AI researchers showed in March 2026 that breaking Bitcoin and Ethereum’s ECC encryption requires roughly 20 times fewer computing resources than earlier estimates, potentially exposing 6.9 million BTC in wallets with visible public keys.
- A future quantum computer running this optimized implementation of Shor’s algorithm could crack a Bitcoin private key in approximately nine minutes, placing every in-flight transaction inside the attack window before block confirmation.
- Google has set a 2029 internal deadline for post-quantum migration, while both Bitcoin and Ethereum development communities are actively drafting PQC migration proposals, making wallet audits a near-term priority for holders today.
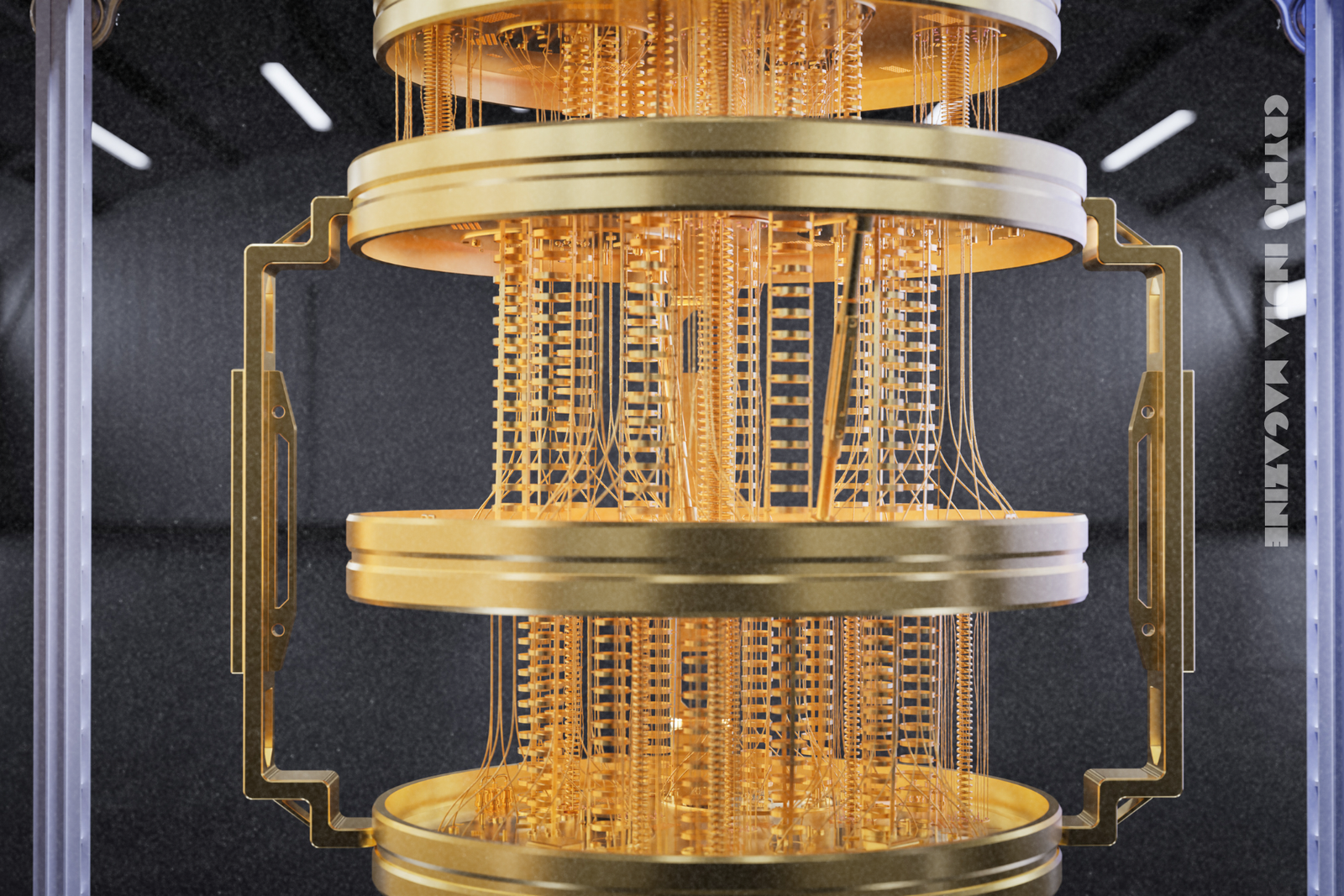
Bitcoin (BTC) and Ethereum (ETH) have secured trillions of dollars in daily transactions for over a decade, and their underlying encryption has withstood every classical computing attack attempted against it. But a new paper from Google’s Quantum AI team has reduced the estimated hardware required to break that encryption by roughly 20 times.
THEREFORE, the timeline for a viable quantum attack has shifted from a distant theoretical scenario to a plausible engineering milestone within the decade.
Bitcoin is a decentralized peer-to-peer cryptocurrency that authorises transactions using elliptic curve cryptography (ECC), a mathematical system that generates paired private and public keys to validate ownership. Ethereum (ETH) is a programmable blockchain that uses the same ECC framework to secure wallets and smart contract execution.
This article covers three key findings from the Google paper, identifies which wallets carry the highest exposure, and outlines the industry’s concrete timeline for post-quantum migration.
What Google’s Paper Actually Found
Google Quantum AI researchers published findings in March 2026 showing that breaking Bitcoin’s and Ethereum’s ECC encryption requires fewer than 500,000 physical qubits and roughly 1,200 to 1,450 high-quality logical qubits.
A qubit is the basic unit of quantum computing, the quantum equivalent of a classical computer’s binary bit. A logical qubit is an error-corrected qubit assembled from multiple physical qubits to reduce computational mistakes during operations.
The new estimate represents a roughly 20-fold reduction from earlier projections, which placed the requirement in the millions of qubits, according to the paper. The reduction stems from circuit-level optimisations and more efficient error correction assumptions aligned with modern superconducting hardware. Superconducting hardware is a class of quantum computing architecture that operates at near-absolute-zero temperatures to maintain qubit coherence long enough for calculations to complete.
Shor’s algorithm is the quantum attack method at the centre of the paper. Shor’s algorithm is a quantum computing procedure that factors large integers exponentially faster than classical computers, enabling it to reverse-engineer a private key from a known public key. The paper describes a significantly more efficient implementation of Shor’s algorithm that requires substantially less hardware than any previous model assumed. This core finding has shifted the industry’s working assumptions.
The 9-Minute Problem: Why Active Transactions Are at Risk
A future quantum computer running this implementation of Shor’s algorithm could theoretically crack a Bitcoin private key in approximately nine minutes, which is shorter than Bitcoin’s average 10-minute block confirmation window.
A transaction is vulnerable from the moment it broadcasts to the network until a miner confirms it in a block. A nine-minute crack places every in-flight transaction inside the attack window.
Alex Pruden, CEO and co-founder of Project Eleven, described the exposure directly:
“A 9-minute crack is faster than Bitcoin’s average 10-minute block time. Every active transaction is a target,” according to a statement reported by The Block. Pruden also noted that Bitcoin lacks the centralized update mechanism that allows banks and governments to push emergency cryptographic fixes overnight.
The paper estimates that approximately 6.9 million BTC held in wallets whose public keys are already visible on-chain are at risk of direct exposure from a sufficiently powerful quantum computer, according to the paper. This figure covers Bitcoin held in legacy address formats where the public key appears permanently in the transaction history, regardless of whether the wallet is currently active.
Taproot’s Unintended Exposure
Bitcoin’s Taproot upgrade increases the pool of wallets whose public keys are visible on-chain. It is the precise input a quantum attacker requires to run Shor’s algorithm against a target address. Taproot is a Bitcoin protocol upgrade (BIP 341) activated in November 2021 that improves transaction efficiency and enables more complex scripting conditions by making public keys visible in the transaction script by default.
The upgrade was introduced to improve Bitcoin’s scripting flexibility and transaction privacy in certain multi-signature contexts. Taproot wallets expose the public key more readily than older Pay-to-Public-Key-Hash (P2PKH) addresses, which keep the public key hidden until a transaction is broadcast. A quantum attacker targeting a Taproot wallet obtains the public key input needed to run Shor’s algorithm without waiting for the wallet owner to initiate a transfer.
Google’s paper urges earlier post-quantum migration specifically because of Taproot adoption growth, while confirming that quantum attacks are not yet imminent as of publication date.
How Researchers and Investors Are Responding
Ethereum researcher Justin Drake described the publication as “monumental,” citing the compounding effect of multiple concurrent improvements to Shor’s algorithm. Drake co-authored the paper alongside Google Quantum AI researchers and Stanford cryptographer Dan Boneh, a collaboration that gives the findings weight across both academic cryptography and the blockchain development community. Drake estimates a small but meaningful probability that a quantum computer capable of breaking elliptic curve keys exists by the early 2030s.
Nic Carter, founding partner of Castle Island Ventures, compared the stakes of the quantum computing threat to the Manhattan Project. Carter’s comparison reflects the broad scope of the risk: a successful quantum attack on ECC affects every system that uses similar standards, including banking infrastructure, military communications, and web encryption protocols.
The Google paper addresses the “it breaks everything equally” argument directly: centralized systems can push software updates to all users; decentralized networks cannot, according to Google Quantum AI researchers. A bank issues an emergency patch to its servers overnight. Bitcoin requires broad network consensus and voluntary wallet migration across millions of individual holders, a fundamentally different operational challenge.
Changpeng Zhao offered a characteristically brief take, stating that crypto will survive post-quantum and that more computing power is “always good,” according to a post on X.
Google’s 2029 Deadline and What It Signals
Google has set an internal 2029 target for migration to post-quantum cryptography (PQC). PQC is a category of cryptographic algorithms designed to resist quantum computer attacks, including lattice-based, hash-based, and code-based schemes that do not depend on the integer factorisation problems that Shor’s algorithm exploits.
The 2029 deadline signals that Google treats this as an active engineering priority rather than a planning exercise. Google operates one of the most advanced quantum computing research programs globally. Google’s internal migration timelines reflect the real resource constraints and institutional risk thresholds that the broader industry will face on a similar schedule.
Bitcoin advocate Bit Paine placed the most likely attack timeline at roughly 10 years, while assigning an “uncomfortably high likelihood” of something disruptive within five years. The shift in language, from “theoretical concern” to a specific probability within a named window, is the most consequential change this paper introduces.
Check Your Wallet’s Quantum Exposure Now, Not in 2029
The Google paper establishes three facts that the industry now accepts. The hardware requirement to break Bitcoin’s encryption is 20 times lower than previously estimated. Active in-flight transactions are vulnerable to a sufficiently fast quantum attack. And Taproot adoption has expanded the surface area of exposed wallets beyond dormant or mismanaged addresses.
Three actions are available to Bitcoin and Ethereum holders today:
- First, identify any wallets using Taproot or legacy address formats where the public key is already on-chain.
- Second, monitor post-quantum cryptography proposals in both Bitcoin Improvement Proposals (BIPs) and Ethereum Improvement Proposals (EIPs) — migration paths are under active development in both ecosystems.
- Third, follow the National Institute of Standards and Technology (NIST) PQC standardisation process, which published its first finalized post-quantum algorithm standards in August 2024, as the baseline reference for compliant migration tooling.
The quantum threat to Bitcoin and Ethereum has always been real in principle. After this paper, it has a specific hardware threshold, a specific attack window, and a specific set of wallets that require action before the threat becomes operational.
Editorial Note: This article was written with the assistance of AI. All facts, figures, and claims have been verified and the content has been edited by our internal editorial team.